The claimant, Nokia Corporation, seeks revocation of European Patent (UK) No. 1 841 268 (“the patent” or “268”) which belongs to the defendant IPCom. This action is yet another stage in the litigation which is pending in a number of jurisdictions in relation to the mobile telephony patent portfolio which IPCom purchased from Robert Bosch GmbH. Earlier this year, the company lost an appeal over another patent claim. The company was seeking to claim EUR12 billion (US$16 billion) from Nokia based on the calculation of 5 percent of Nokia’s mobile phone sales in countries covered by the patents, or EUR 600 million (US$840 million) a year over 20 years.
Nokia had been seeking the revocation of European Patent (UK) No. 1 841 268 (‘268 Patent) belonging to IPCom. In addition, by counterclaim, IPCom alleges infringement of 268 in respect of a number of mobile phones sold by Nokia. Nokia denies infringement. The ‘268 patent is itself a patent which was divided out of European Patent No. 1 186 189 (“the parent patent”). Like the parent patent, ‘268 is concerned with managing the problem of contention on a random access radio channel uplink between mobile phones and a network base station.
Regarding the validity of the patent, Judge held that “It is of course always necessary, at the end, to take a step back and ask whether the claim embodies an inventive step, both in the case of the attacks based on specific publications and in the case of the common general knowledge. Nokia submitted that the invention achieved nothing in terms of functionality as compared with, say, IS-95. That is correct as far as it goes, but it does not follow that IPCom’s approach to achieving that functionality is obvious. It is entirely possible that invention lies in achieving the same functionality in a different way. In the end I was not satisfied that any of Nokia’s four starting points rendered IPCom’s solution obvious. It follows that I reject all the attacks on the 268 patent based on obviousness”
Infringement
There is a Product and Process Description for each of 14 types of Nokia device. The High Court held that the ‘268 Patent was infringed by two Nokia devices: “the A1″and “the A2″,but Nokia were granted a declaration of non-infringement in respect of Nokia’s devices, labeled B1,B2,C1,C2,D1,D2,E1,E2,F1,F2,G1 and G2.
High court clearly analysed the infringement by mapping the features of devices A1 and A2 of Nokia with the Independent claim 1 of ‘268. Independent claim1 of ‘268 patent is broken as follows:
[A] Mobile station for operation in a UMTS mobile radio network
[B] in which multiple user classes are distinguished
characterised in that the mobile station is arranged
[C] to read a user class from a SIM card
[D] to receive access threshold value bits and access class information over a broadcast control channel
[E] to determine an access threshold value from the access threshold value bits
[F] to use the access class information relevant for the user class to determine whether
[G] the mobile station is permitted to access a random access channel, for example RACH, independent of the received access threshold value bits
[H] or whether the access permission for the random access channel, for example RACH, is determined on the basis of an evaluation of the access threshold value.
Infringement
- The Nokia device described as A1 operates as follows. The mobile is designed to receive two parameters of relevance. These are the dynamic persistence level, N, and the AC to ASC mapping information.
- Any device operating in accordance with the A1 method must be a member of at least one Access Class (AC). There are 10 normal ACs, numbered from 0-9. Every device must be a member of one of those normal ACs and the number of the particular AC to which the device belongs is stored on its SIM card. There are another 5 special Access Classes (11-15) designated for use by special groups of users such as emergency services and network staff. All access classes may be barred at any time by the network.
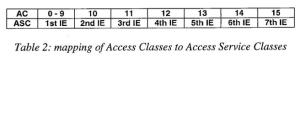
- The next thing which it is necessary to understand is how the A1 selects an Access Service Class (“ASC”) which it will use for its access attempt. These ASCs are different from the AC stored on the SIM.. The transmitted data includes an element entitled “AC-to-ASC mapping”. This allocates each AC to an ASC. There are 8 ASCs numbered from 0-7. The mapping is carried out by the device reading the information element (IE) in the System Information Block appropriate to its AC. The way this is done is set out in Table 2 taken from the A1 Product and Process Description. ACs 0-9 look at the first IE in the block, 10 the second, 11 the third and so on.
- Depending on which ASC has been allocated by the mapping process, the device works out a “persistence value” known as P(i), (not the same as the dynamic persistence level, N, sent by the network). The way this is done is set out in Table 1 taken from the A1 Product and Process Description.
- It can be seen that there is a difference between ASC 0 and the other ASCs. If a device is in ASC 0 the device automatically sets its persistence value, P(i), to 1. This conclusion is arrived at directly from the AC to ASC mapping and not from the other parameter of importance, the dynamic persistence level, N.
- On the other hand, if a device is in one of the other ASCs (1-7), it has to carry out a calculation using the dynamic persistence level, N, sent by the network.
- So P(N) is a function of (i.e. mathematically dependent on) the transmitted dynamic persistence level.
- Devices which are mapped to ASC 0 by the network will automatically pass the persistence test because the random number can never exceed 1. Those devices which are mapped to ASC 1 or higher may or may not pass the persistence test. Whether they pass the persistence test depends on the value N sent by the network.
The judge held that Nokia device A1 in summary held that:
i) the bits used to transmit the dynamic persistence level, N, constitute the access threshold value bits;
ii) the AC to ASC mapping information constitute access class information;
iii) P(N) is an access threshold value which is determined from the access threshold value bits;
iv) the AC to ASC mapping information is used to determine whether the device is in:
a) ASC 0, in which case it is permitted to access the RACH independent of the received access threshold value bits because it has a P(i) value of 1 which is not a function of the persistence level N which is being broadcast by the network; or
b) an ASC other than 0 in which case it must determine access permission on the basis of an evaluation of P(N) which comprises a comparison of P(N) with a randomly generated number.
In the A1device the random number comparison gives a win/lose determination on permission, whereas in the A2 it determines the extent to which permission will be delayed. However, the judge held that, in both cases access permission is determined on the basis of an evaluation of the access threshold value and thus infringing ‘268 patent.
About the Author: Mr. Veera Raghavan, Patent Specialist at IIPRD and can be reached at: Raghavan@iiprd.com